Everyone wants secure communication without any third-party involvement. Cyber attackers are the primary reason for the hunting for our data, so it was necessary to introduce cryptography to stop attackers from stealing our data for their purpose.
Encryption ensures data and information security from unauthorized access and maintains confidentiality. Here, we will help you understand what cryptography is and how it can be used to guard our personal information against cyber theft.
Let’s understand what cryptography means with an example.
Must Read: Importance Of E Commerce Cyber Security For Merchants
What Is Cryptography?
Cryptography is the art of securing your communication; secure in a way that no one except the receiver could watch it.
Let’s consider an example: Suppose you want to send a message to your friend who lives on the other side of the world. You want this message to be private, but you use a public platform like Whatsapp to send the message. By this, how can you secure your communication?
Anyone can access your communication channel, and the person can try to change your message. Due to these actions, the concept of encryption or cryptography network services was introduced.
The practice and study of techniques for securing your communication and information over a network is the goal of cryptography security. Let’s move on to see how cryptography network services work.
Suggested Reads: Top Examples Of Ecommerce Payment Solutions
How Does Cryptography Work?
We will understand this by referring to the above example. Let’s see how you can secure your communication with your friend.
So, to protect your message, there is a thing called ciphertext, which encrypts your readable message into unreadable form. You need to send this encrypted string message to your friend, and there he will use a decrypted string key to convert the message into its original format. This process helps you communicate with each other without any intrusion from other people.
Based on the keys and encryption algorithms, cryptography has further classifications. Let’s discuss them.
Encryption algorithms
Want to know the classification of cryptography? Let’s explore with the below figure.
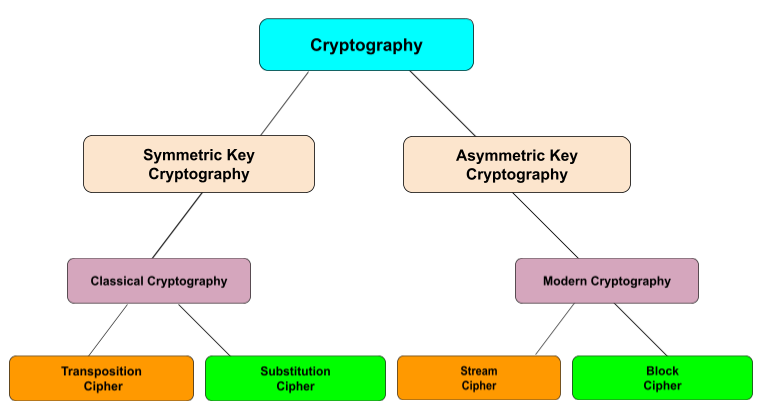
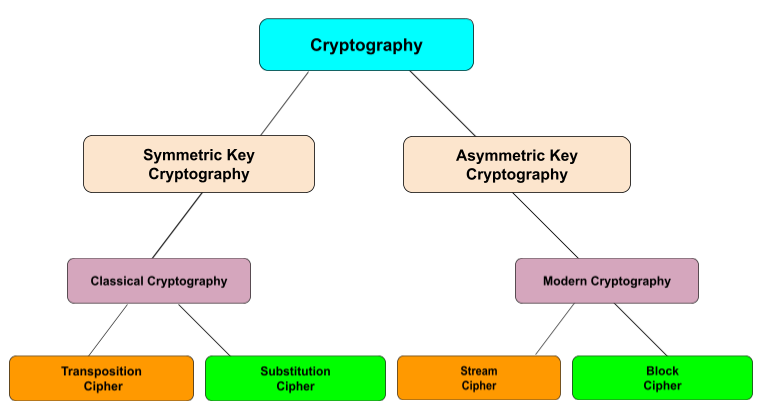
Let’s understand these algorithms for your better understanding.
Also Read: Payoff For India’s Unicorn Revolution: How Unicorns Are Lifting The India’s Startup Ecosystem
How Do These Various Cryptographic Algorithms Work?
To see what it means to access cryptography security, take a look at these cryptographic algorithms.
- Symmetric Key Cryptography: an encryption method in which both sender and receiver share a single, common key for encrypting and decrypting the message during their communication. For example, Data Encryption Standard (DES) is the most popular encrypted key system.
- Transposition Ciphers: an encryption method in which the order of alphabets in the plaintext in cryptography is rearranged to form a ciphertext.
- Substitution Ciphers: an encryption method in which units of plaintext in cryptography are replaced with the ciphertext in cryptography, in a defined manner, with the help of a key; the “units” may be single letters, pairs of letters, triplets of letters, etc.
- Asymmetric Key Cryptography: an encryption system in which both sender and receiver share different keys to encrypt and decrypt the message. It is also called public-key encryption.
- Stream Cipher: an encryption method that uses a symmetric key to encrypt and decrypt the given amount of data.
- Block Cipher: a process of data encryption into blocks to generate ciphertext in cryptography using a cryptographic key and algorithm.
Also Read: Ecommerce Is Big In India, But The Industry Needs To Battle With Fraudulent
Final Words
Cryptography network services help achieve information security by guarding data against cyber attackers. Cryptography security ensures transactions and communications in modern security systems and safeguards personally identifiable information (PII) and other confidential data. Because when your data is encrypted, an unauthorized user cannot gain access to it.
Cryptography ensures secure services in cash withdrawal from an ATM, safe web browsing, etc., thus, we can say that cryptography is the solution to many unsecured services available on the internet.
Recommended Reads:
Introduction To Augmented Rooms Using Metaverse By Amazon
Amazon SEO Or PPC – Who Steals The Competition?
Check If These Measures Are Absent In Your Ecommerce Website (For Beginners)










Leave a Reply